Jaymes Nowicki, SVP Director of North America at Intaso, had the pleasure of sitting down with Michael Myint, former CISO at Publicis Sapient, and Waltz Health, and is now leading the greenfield cybersecurity program at COTA.
During the conversation, Jaymes and Michael discussed everything from the changing landscape of technology to predictions to the future.
About Michael:
Michael is a seasoned Chief Information Security Officer (CISO) with over 25 years of experience in Cyber and Information Security. His leadership has been demonstrated across various industries, and he has developed expertise in crafting and implementing robust security programs, ensuring compliance with industry standards, and mitigating evolving cyber threats.
At Publicis Sapient, he led a global security team, streamlining risk management processes and securing service delivery for over 400 clients worldwide. His strategic initiatives showcased his commitment to enhancing overall organizational resilience in the face of cyber threats. At Waltz Health, he orchestrated a transformation, elevating the startup’s security posture from non-existent to best-in-class.
Now at COTA Healthcare, he is their first investment in cybersecurity leadership, responsible for driving the development of a greenfield cybersecurity program. Michael is a proven cybersecurity leader whose extensive experience, technological acumen, and vision make him an invaluable asset for any organization aiming to fortify its cybersecurity landscape.
Foreword from Jaymes:
It took a colleague located thousands of miles away and in another country for us to be introduced. One initial discovery meeting evolved into talking weekly, for almost two months. During this time together, we dove deep into his career journey and covered many topics. By the end, we’d formed a trusting professional relationship, and I found myself advising on his search to find a new home.
What I found is that Michael is a Cybersecurity Leader and Subject Matter Expert who loves building and solving problems. He is authentic and genuine. He keeps his ego checked. Even after more than twenty years in cyber and information security, he is as passionate as his first year in the industry, and extremely excited about the future.
Michael, it was a pleasure getting to know you. Thank you for investing so much time and effort in this.
Jaymes: First, I’d like to talk about your journey into cybersecurity. How did you arrive in the industry and what drives you to stay?
Michael: Well, I graduated with a Bachelors of Science in Marketing. My first career job was at Andersen Consulting and back then, they would send all ‘Early Career’s’ through their Technology bootcamp at their world-wide training center. I learned how to code in VB and Lotus Notes and started building websites and portals for clients. Traditional methods for protecting Internet/Intranet sites and Identity Management came into play.
I spent the next decade or so building out security solutions while at a few of the Big 4, becoming a SME in Identity and Access Management and Network Security. During that time, I developed a passion for building security programs and teams for both small and large companies.
What drives me to stay? The reason I’m still in Cyber almost 30 years later is because I enjoy the ever changing landscape of Technology; this past decade or so it has been a journey from Data Centers to Cloud, the introduction of smart phones and smart devices, and recently leaps and bounds in artificial intelligence (AI) and large language models (LLM).
I wouldn’t say that AI brings to us new threat vectors, more so that it will require deeper consideration of existing threats. Advanced Persistent Threats (APT) and Impersonation of human language in voice, text, and potentially visualization will greatly increase sophistication in malicious automation and social engineering.
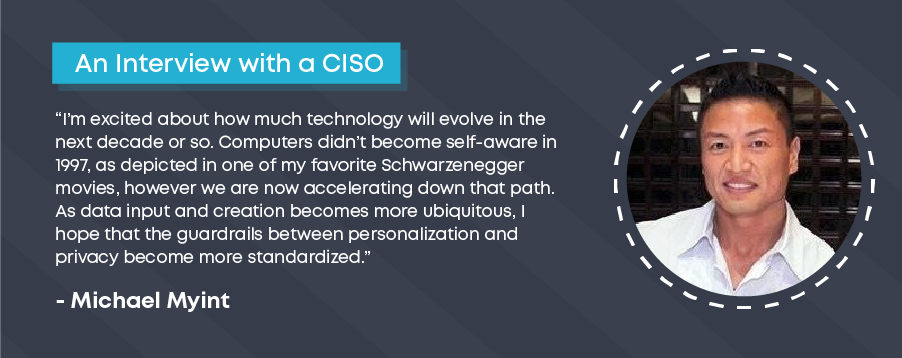
I’m excited about how much technology will evolve in the next decade or so. Computers didn’t become self-aware in 1997 as depicted in one of my favorite Schwarzenegger movies, however we are now accelerating down that path. As data input and creation becomes more ubiquitous, I hope that the guardrails between personalization and privacy become more standardized. It’s hard enough educating folks in my generation of the risks involved in interacting with websites and apps, it’s even harder to convince my kids that I know what I’m talking about!
You had the opportunity to function as a Global CISO with Publicis Sapient and an early-stage CISO with Waltz Health. How do you think spending seven years in security leadership at a global company impacted your approach and strategy when joining an early-stage start-up?
I think being at a large company for that long shaped my approach to always partner first, and make sure my security objectives are aligned and support business objectives. Once I’m able to assess Leadership’s security awareness and receptiveness, I use that knowledge to fine-tune the security roadmap. I recognize in an early-stage that getting the MVP out and achieving ARR is the priority, so I try not to cause a lot of friction with timelines. I look for quick wins with implementation of security controls that are easier to swallow for the rest of the organization.
At Publicis Sapient, the Enterprise Security/GRC side of the house was mostly BAU (business as usual). We had our regular policy review and updates, Compliance support (regulatory readiness, client audits, external audits), Third Party Risk Management (TPRM), Internal Assessments, Training and Awareness, and BCP/DR. Handling this side of things was about streamlining automation where possible, and cutting out unnecessary activities.
Now, on the Cybersecurity side of InfoSec, that was a bit more fun! We got to deploy DLP and CASB, SAST, DAST, and IAST, VAPT, and PIM/PAM.
When I joined Waltz Health, now being in a regulated industry, I first focused on training, compliance, and implementation of basic security hygiene. Another priority right after that was visibility, so I outsourced a SOC/MDR and deployed a CNAPP (cloud native application protection platform) solution. Immediately after, I worked to add Security into the DevOps pipeline. The plan was to establish governance, layer SAST and DAST into the pipeline as well as set policies for container hardening.
Having experience in building a security program at two organizations, solidifies my belief that regardless of organization size, you have the same threats to protect against. The foundations of a security program doesn’t change. We’ve all been taught a consistent and scalable approach. What will differ is how we align to the business roadmap and make it sustainable, whether in a fast-paced, rapid-growth environment, or extremely large and complex environment with a moderate pace of change.
There are a lot of early-stage SaaS companies that invest in a CISO too early, and some too late. What is your opinion on when the time is right?
I think if the company is in a regulated space, they should invest in a security leader as soon as the MVP is ready. Shortly into the game, clients will expect that you have your ducks in a row, and that you’re compliant with the respective regulation for your industry.
I understand a lot of considerations have to be sidelined momentarily, however if you’re providing a solution, you have to make sure it is secure. If the company is not in a regulated space, they should bring on a security leader when they are prepared to invest appropriately, in both the staffing and tooling. Early-stage companies must be aware that they are targets of malicious actors as soon as their existence is publicized.
With or without a CISO, they should establish protections for people and identity right away; endpoint protection, secure email gateways, multi-factor authentication, VPN connection into the product environment (and add an extra hop if you can!)
Early stage companies are not investing to bring on CISO capabilities at a VP level or above. Most are hiring for a Director to lead the program with expectations to perform the tasks of a Security Engineer, in addition to the Strategic and Tactical needs. I think this is a bad approach, and lack of understanding from members of the Engineering and Product teams.
Having a security leader with the soft skills to negotiate and influence the ELT, Customers, and other Third Parties is essential. There needs to be influence on the budget. The organization will recognize dividends on this hire when he or she helps them navigate and contain a security incident. A low-severity incident can avalanche into considerable financial losses if poorly managed. All it takes is one significant security incident to consume too large a portion of your most recent round of funding that it can curtail business objectives. I would even suggest that what you spend on Cyber insurance should be multiplied 3-5 times to budget for your information security program; at least with 2023 market rates.
There is a lot of reporting about how shifting economics have led to reduced VC investment into cybersecurity SaaS vendors. For early-stage companies, being positioned to secure new funding is critical. How can CISOs help close on new rounds of funding?
They’ll need to illustrate that the company has a strong security posture and communicate the 1-3 year security roadmap aligned to business objectives. 3rd party Penetration Testing of the MVP and other iterations to show that the product/solution is secure.
If applicable, achieve regulatory compliance and successfully pass a third-party review.
Build relationships with the Board and potential Investors, be a part of the pitch team.
Can you share with me your experience, interest and passion for greenfield initiatives, specifically building cyber programs and teams from the ground up.
I love building! Who wouldn’t want to design their dream house or dream car? But even better than that is the satisfaction of building something from scratch, that proves tangible benefits for those that invested in you.
Although it was very satisfying improving the security posture and developing security capabilities that enhanced revenue creation for our Digital Transformation services, that was like navigating a barge through a narrow canal for a large organization. In a greenfield start-up, you have to prioritize intelligently, get quick wins, and establish the pillars of a security program quickly. Some areas may have best-in-class tools, while others are manual and process heavy. At Waltz Health I tackled security awareness, endpoint protection, and infrastructure visibility first. Next, I focused on DevSecOps and Vulnerability Management. This path enabled us to rapidly build an information security management system to obtain regulatory compliance and achieve SOC 2 Type II, with all 5 trust criteria.
One of the areas I really enjoy in my own growth is mentoring others. If you can’t share your lessons learned with others, the environment is doomed to repeat the same mistakes and lose out on valuable time. I’ve had a lot of learnings and was trained vigorously when I worked at the various Big 4 consulting organizations. They nurture the Type A personalities and polish you to be a Team A player.
There are definitely some trade-offs with that, however. In more recent years, they are seeing the value of, and balancing the EQ contributions to success. My point is that I also learned from the cold competitive harshness of those cultures to be more nurturing to members of my team. I’m very hands-on and will schedule as many working sessions as needed with members of the team. I feel it helps to think out loud as you’re working through the creation of deliverables together.
There are so many areas in an Information Security program, that I often give ownership of each objective to a specific person. When we have tangible results and success that gets attributed to them, if we have bumps in the road for whatever reason, I take ownership of that. At the end of the day the buck stops with me for any issues. I take pride in the accomplishments of people that I have mentored and/or been on my teams. Many of them are very successful today and have exceeded my success; founders of new technology companies, fellow CISO’s, CIO’s, and even one CEO of a public company in the security space.
What is your process for developing a cyber and information security roadmap?
I feel security awareness and phishing training is low hanging fruit that you can get kicked off quickly and mature as time permits. Depending on organizational size, and since I used one recently, a Compliance SaaS tool sure saves a lot of time in evidence collection and automation for passing an Audit. IT should have endpoint protection already addressed, so the next item should be visibility on the network, simplest path for this would be to outsource an MDR service. GRC and cybersecurity activities should be happening in parallel!
One of the biggest challenges a CISO has is getting buy-in from the company board and leadership. How do you go about this successfully?
I clarify expectations and set the tone during the interview process. I don’t want to get myself into an organization that is not ready to support a security program. Even in a start-up, the leadership should have been around the block enough to have gone through a negative finding in an external audit or have experienced a material security incident.
What was the board interaction like at Publicis Sapient? And how was that different at Waltz Health?
At Publicis Sapient, the “Board” is the Management Board from the parent company. Their goal was collaboration across the various agencies bringing forth “The Power of One” to provide full stack services to clients, from Creative to Media Management to Digital Transformation and much more. When updates were provided to the board, that was done jointly between certain officers of PS and our shared services organization; I would just help with building some content on the security posture and roadmap, and sometimes include a synopsis on the most visible and impactful security incidents that occurred. Budget approvals were managed internally by our CFO, and I would manage the creation of the deck for our quarterly updates to the leadership team and navigate through various slides in carillon with other stakeholders.
At Waltz Health, various board members would visit us onsite on a regular basis. Two members of our ELT sat on the Board to which I would give both ad-hoc updates as well as quarterly updates on our progress against the roadmap. During the quarterly updates I would make my financial requests and align the tactical initiatives against the business timelines. I would reinforce my requests during ad-hoc, watercooler conversations to get a gauge of their understanding of my proposals in support of business needs – for Execs, this is the benefit of hybrid return to office, you can’t time a casual bumping into someone in the break-room when you’re virtual!
What I learned is, when possible, reinforce your ideas and requests in as many informal situations that you can. Direct one-on-one conversations outside of the large audience setting will help you get further, so make sure to nurture those relationships.
Can you share experiences of your most important lesson learned, and your highest of highs?
When the Pandemic hit, I helped to ensure that we could continue delivering Digital Transformation services to our clients as we quickly adapted to work from home. We established Global and Country-level governance teams and monitored the rapid and dynamic-evolving, global situation across governments and health organizations.
To better enable our mobile workforce, we deployed our Business Continuity plan, which included:
- Expanding our VPN infrastructure
- Increasing bandwidth
- Stood up more connections to reduce hops
- Moved endpoint management over the Internet so we could manage devices even when off VPN
- Enhanced SOC capabilities to monitor traffic from remote VPN gateways
- Increased VDI capabilities to support continuation of new hire onboarding
- Implemented more data security controls
Of course, our top concern was employee safety, followed by client delivery. I feel strongly that our efforts limited the impact of Covid, while also improving our revenue performance over the subsequent two years that followed. We demonstrated to our clients that we were nimble for an organization our size, and still able to deliver and evolve their services to consumers to meet the shift in consumer to business interaction.
What are some mistakes you made, and what challenges or problems did you face as a result of your decisions? How did you overcome that and what lessons did you learn?
One of my toughest ‘lessons learned’ was the low adoption of rolling out a Privileged Identity/Access Management (PIM/PAM) solution. As a best practice, and from issues we’ve had with hard coded secret keys “accidentally” being posted to public repos, it was a no brainer to have the capability.
Unfortunately, we moved too quickly to deploy and didn’t invest enough time to spread awareness and educate our Engineering community on leveraging the tool. Add to that, the complexities of working in various client-managed production environments, we would then have to architect the solution and contractually define ownership and appropriate licensing on a project by project basis. My appetite for success was too large in this case, that I didn’t account for all of the nuances of architecture and all of the dependencies in the software development lifecycle.
What do you think are the top three critical areas or threats that organizations, no matter the size, need to be in front of?
- Phishing
- Identity compromise
- Endpoint protection
Notice this all relates to people?
Training and awareness needs to dramatically evolve. Understandably, most organizations have the 2-3 hours required annually, where we have to move to quick 30-120 second engaging content on perhaps a bi-weekly basis. That content should educate people on phishing, protection of identity, and protection of data on their devices.
As security practitioners, we’re constantly deploying solutions to protect people from all of those vectors with EDR, MFA, VPN, Password Vaults, PIM\PAM, etc, whereas great training is the most cost-effective solution. I, myself, try to wrap my workforce in an invisible bubble that doesn’t interfere with their natural behavior, however, as time permits we must evolve the culture to have security baked into their daily habits.
Over the past year, many organizations have sidestepped and prioritized cybersecurity less. Why do you think this is?
I think this is happening on two fronts; the small start-up organizations and large mid-caps.
It’s interesting that large companies have requirements for their customers to have stronger security programs in place. Every MSA I have seen in the past 4+ years now has a Security Addendum. You generally have a Master Services Agreement that you negotiate on with each client. These should be reviewed by your GRC (Governance, Risk, Compliance) team to catalog security requirements and make sure you are in compliance as part of your internal risk assessments.
By the way, I would label non-compliance to contractual requirements as a “High” severity. And as I mentioned, as MSA’s evolved, they started having Security Addendums which were more robust security requirements. This is similar to the Healthcare sector’s BAA’s (Business Associate Agreement) to covered entities. You will see this expectation from every Global 500 and likely every Global 1000.
And, even with this expectation in place, many large companies have found it ok to reduce their security workforce. They’re just not feeling the consequential repercussions enough when even in some cases they’ve had notable information security incidents. Honestly, I don’t get it… it’s odd!
The smaller companies are much more laissez-faire, and often run check-box exercises. There’s not as much leadership support, financial support, evidenced by how they staff for Security. Companies that are pre-IPO are more concerned (appropriately) with proving value of their product or service so their heavy investment is typically in Engineering and Product.
Unfortunately, they won’t recognize the need for Information Security unless they have a regulatory requirement or fall victim to a security incident. There is some awareness of the need for a Security Leader, but again, the investment in this area is limited.
Thank you for taking the time to talk to me today, Michael. Where can people connect with you?
If people would like to connect with me on LinkedIn, I’m always looking to speak with like-minded professionals!








