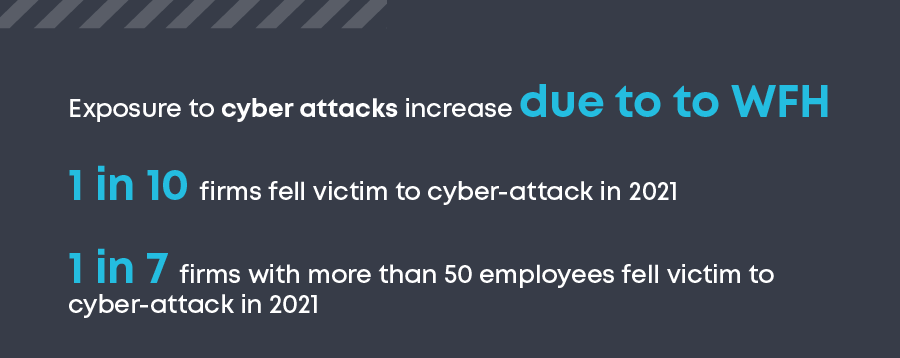
When the UK first went into Covid-19 lock down in March 2020, many companies were forced to embrace the idea of their employees working from home (WFH). Even for companies which had previously supported a measure of WFH, the scale and speed of the change was unprecedented. It is perhaps not surprising then, that a recent survey from the British Chamber or Commerce reported the that more than half of firms believe their exposure to attack has increased due to working from home arrangements. It also revealed that one in 10 firms have been the victim of a cyber-attack in the last year and that this rises to more than one in seven for larger firms with more than 50 employees
These results are not unique to the UK, however. Deloitte surveyed 1,500 Swiss residents of working age and asked what technological challenges they face as a result of working from home, how they judge cyber security, and how they themselves act in terms of security. Whilst 90% of respondents thought that their employer’s cyber and data security measures allowed them to work efficiently from home, one in four stated they had seen a rise in phishing, spam and fraudulent e-mails whilst 26% reported they were tempted to keep copies of valuable company data, in case ‘the worst comes to the worst’.
Working from home created more cyber threats, but why?
Over the past decade, almost all businesses have realised the importance of some level of protection against cyber threats and attacks. However, in many cases focus on enhancing cybersecurity has assumed a working-from-office model, with WFH being a managed exception for a limited period. Traditional cyber security measures focused on ensuring suitable technological infrastructure and adequate cyber and data security in the office environment. With the almost instantaneous move to home working, there was little time or resource to focus on ensuring even basic measures, such as appropriately securing Wi-Fi, was possible. Hacking a home network became a very real, and in some cases very rewarding activity, especially if employees were keeping local copies of valuable data.
However, there were bigger cyber risks emerging. The need to suddenly roll out new online tools for collaboration and productivity brought with it increased cyber crime opportunities. As early as April 2020, the FBI warned that video calls were getting hijacked. Zoombombing, as it came to be known, was born. It was not just Zoom that suffered. The default security settings for many online tools and services are often the bare minimum and updates from third-party vendors can change security preferences. In the distributed IT environment that WFH delivered, traditional cyber security models were found wanting. Cyber criminals were only too happy to exploit the vulnerabilities.
Yet even this was not the biggest cyber crime opportunity. Phishing scams rose exponentially, with Barracuda noting a 667% increase in spear-phishing attacks in one month alone. KPMG also saw “evidence that remote working increases the risk of a successful ransomware attack significantly.” But why should phishing attacks and ransomware be so much more effective in a WFH model?
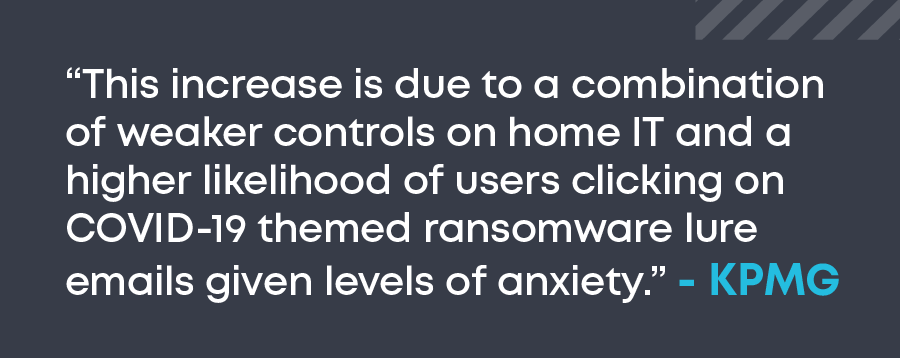
At the most basic level, the success of these scams is based on a user clicking on something they should not. In a distributed working model, the ability to easily query adjoining co-workers is lost. The ‘have you got one of these emails too?’ first level of checking is missing. It is more difficult for workers to get assistance from the right experts and support teams too. Evidence, however, suggests that reporting of such incidents is scarce, believing that they can either deal with the issue themselves or that reporting an incident will have a negative outcome for them. Humans have always been the weak link in IT security, and the working-from-home model made that vulnerability easier for criminals to exploit.
What can be done to reduce the impact of cyber threats when working from home?
Working from home will be with us for forever, so how can organisations protect themselves from the increased cyber risks? If humans are the weakest link in the chain, then that is where the solution needs to start. Regular education and training on what a phishing attack looks like is important. Equally, understanding what to do if a user does click on a suspicious link or downloads a questionable file. Perhaps the most important change that needs to be made is creating a no-blame culture where employees are comfortable and able to report immediately when they have made a mistake, or suspect something is wrong.